Is There a GPU I Could Use to Crack a Random 8-character WinZip Password In Just One Hour?
We got this question from a user who is testing Accent ZIP Password Recovery.
 |
Accent ZIP Password Recovery for Zip/WinZip archives with classic and WinZip AES encryption |
22.01 | Download x86 (7452 Kb) |
Download x64 (8956 Kb) |
| ||||
To cut the story short, there is no such GPU on the market today. So cracking a strong protection password (AES encryption ensures strong protection of WinZip passwords) is impossible. The only option is to password recovery.
And you will see why.
Password Cracking Explained
Cracking a password is, in fact, searching for the right password from a defined range by brute forcing.
While you are setting the range, you customize password length and the number of characters in it. The bigger a character set and the longer the password, the more combinations will have to be tested.
Number of generated password is calculated by the formula:
number_of_characters_that_ can_constitute_password password_length
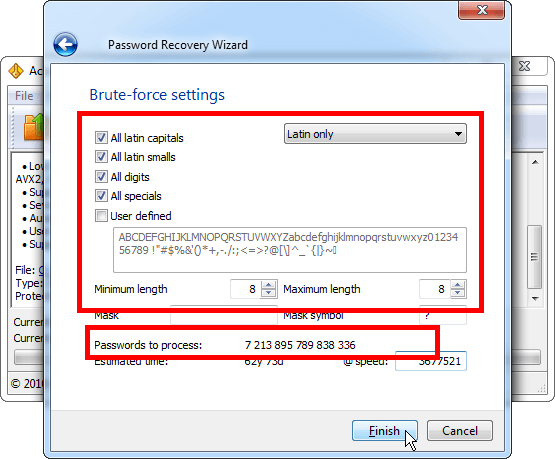
In the case of a random password, of which you do not know anything, you will have to include all printed characters into the range. If you take ONLY English keyboard layout, then together with special characters you will get the total of 96 characters (52 uppercase and lowercase letters, numbers and special characters).
In that case, the number of characters of an 8-character password will be calculated as follows:
96 8 = 7 213 895 789 838 336
In order to test them all in one hour, the speed should be 2 003 859 941 621 passwords PER SECOND (divide the number of passwords by 3 600 seconds of one hour).
Now then, what do graphics cards offer?
Here at Passcovery website we have a GPU ranking and comparison chart, permanently updated for you. See the list of most efficient GPUs based on the performance of Passcovery applications.
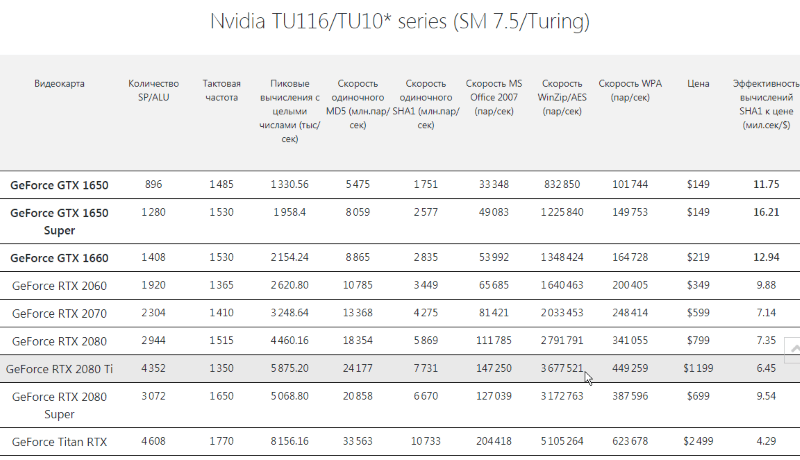
One of the most efficient video cards for brute forcing WinZip passwords is GeForce RTX 2080Ti. It performs at about 3.6 million passwords per second (under ideal conditions) or 12 960 000 000 passwords per hour.
If we divide the number of generated passwords by the hourly performance of one video card, we will see how many hours it will take to sort through the entire range of passwords:
7 213 895 789 838 336 / 12 960 000 000 = 556 627 hours
In other words, to crack a random 8-character password in one hour you will need a GPU farm of 556 627 GeForce RTX 2080Ti graphics cards that would all be searching for a single password.
Using the data from our GPU rating chart, you can calculate how big a farm it would take to crack passwords of various length.
Password cracking – impossible. Password recovery – probably
Well, that is actually what strong protection is all about: with no password, cracking a file in order to get access becomes impractical and even impossible.
It takes too much time and money.
That is why it is impossible to crack a file with strong protection. The only option is to recover the password.
To do this you first need to collect all you know about the password: its structure, precisely and hypothetically known parts, characters. That enables you to cut off false passwords, significantly reduce the range of generated words and reach successful results in reasonable time.
Here is what Accent ZIP Password Recovery (or any other Passcovery program) can do with the same kind of WinZip archive, protected by an 8-character password.
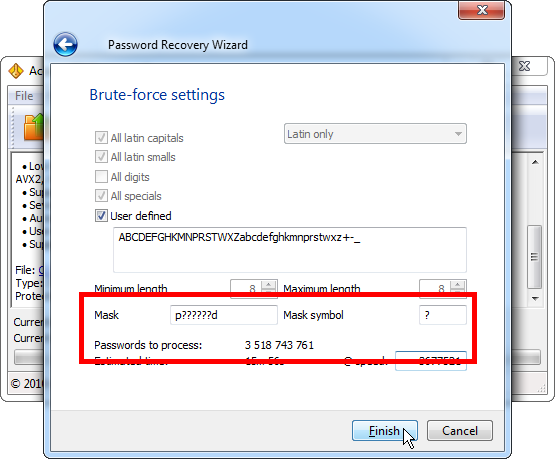
1. Brute force attack with [not] used characters
For example, if you know that a password uses only a certain number of special characters (+-_), does not contain any numbers and letters looking similar to numbers, then you can reduce the number of characters that make up the password from 96 down to 39. The range then gets 1 313 times shorter.
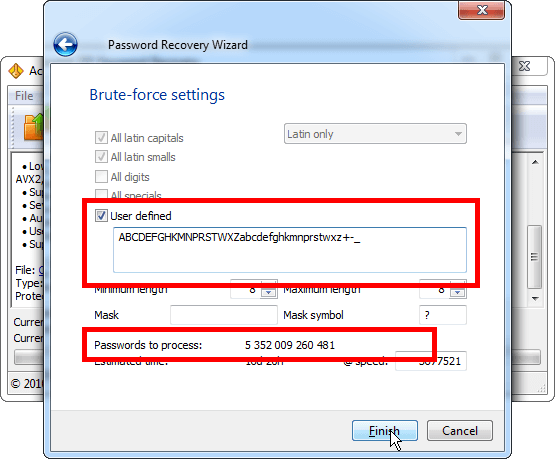
Please note: by reducing the number of characters, you shorten the range of generated passwords and speed up the process.
2. Brute-force with mask attack
When you know exactly some parts of the password, you can define a mask and boost the search speed.
3. Brute-force attack with extended mask
If you know the password structure and possible characters in each position (the first character is a capital letter, there is a lowercase letter in the middle position, and the last character is a special character + -_), then Passcovery programs will help you define such a tricky mask and successfully recover the password.
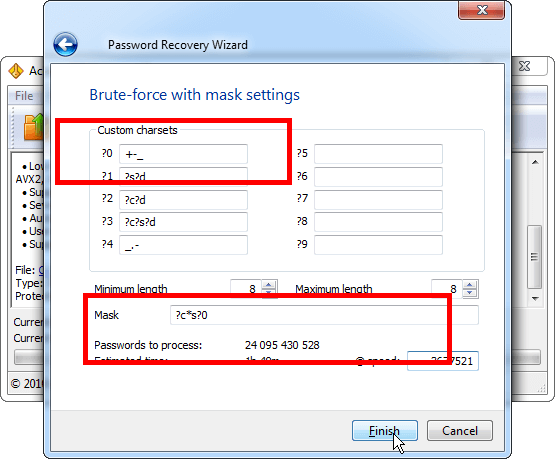
See more examples of using extended mask here.
Strong Protection and Weak Password
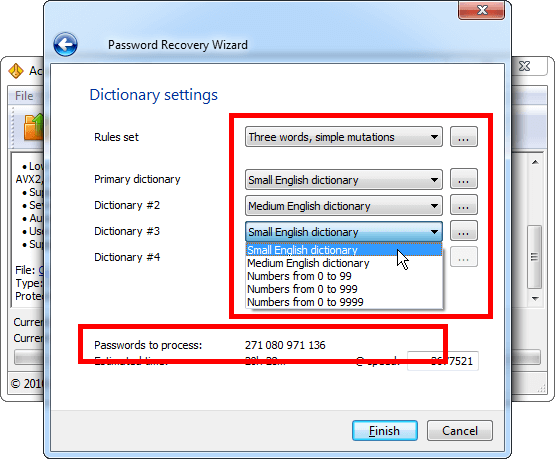
Though password protection is important for all, still many people create weak passwords that are easy to guess. Such cases will always be there.
A weak password may be just a word, any of its simple forms, or a word combination. Most likely, such passwords have long been found and added to the dictionaries of weak passwords. You can find many of them on the web (see example).
Hacking a WinZip file (or any other format) with a weak password will not be a problem.
Accent ZIP Password Recovery (like all Passcovery programs) offers advanced dictionary attack: it can simultaneously work with 4 dictionaries, glue passwords into one, modify the resulting password and test it.
Needless to say that it performs all these functions at the maximum possible speed.
Conclusion
Graphics processors can significantly speed up brute force attack. However even the best of them are not capable of cracking a strong password with strong protection.
In that case you could only recover it using every bit of information about the password.
That is how password cracking is different from password recovery.
- Cracking implies hacking somebody else's password of which you know nothing. It is a dead-end road.
- While recovering a password you searching for your own lost password. Any small nugget of information, anything you can remember helps shorten the range of possible passwords, perform a swift brute force attack and hit the right one in the end.



