Passcovery on the Myth of Hidden Threat
With reference to an emotional response from a frustrated AccentOPR user we’d like to once again speak about the users’ concerns and the runtime of our password recovery tools.
“I was trying to unlock one of my old files but I ended up cancelling. It was taking AccentOPR awfully long to finish the search. Actually it looked more like it was scanning the whole of my hard drive, while the size of the file is only 100kB. That looked a bit fishy to me. What was that all about?”
Author of the photo — @denglad
Well, first of all, there is absolutely nothing to fear or worry about.
And here’s why:
- We, Passcovery team, represent a totally legitimate company from Russia established in 2008.
- 2. The first edition of AccentOPR was released as early as in 1999.
- 3. All software products at our website are certified with the digital signature of the company.
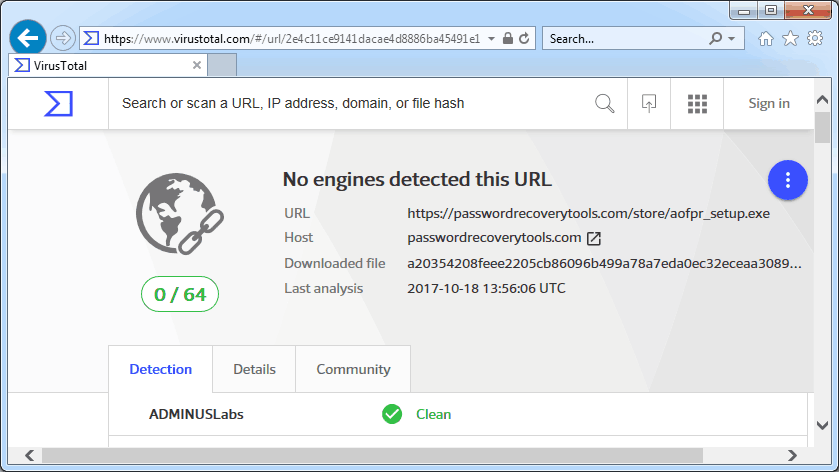
- 4. A check on the Google service virustotal.com has proved [of course!] there is no malicious code in our programs.
We value our reputation and care about our users. Therefore, you will not find any hidden threats to your computer in any programs downloaded from Passcovery websites. No threat, no fret!
Once again about time…
There is no miracle in our programs. Yes, they are quite fast. And yet the searching process may get dragged out for a while…
Let us get this straight. The password to be cracked is unknown to either you or the program. While searching for the password the program tries every password combination in a range (or dictionary) specified by you. The number of combinations, which can be millions and millions, depends on the number of characters used for generating each combination (or a dictionary size and mutation rules).
A file format also affects the search time. For example it takes way way longer to find a password for an Microsoft Office 2013 file than that for Microsoft Office 97. Find detailed information about different Microsoft Office editions and specifics of password recovery here.
So it turns out that recovering a password takes time, processing capacity and a bit of patience.
The program neither stops responding not starts scanning your hard drive. It’s just working – recovering your password by trying each word one by one.
How to boost password cracking
Is there any way to cut the search time?
Sure! Reduce the range of values to be checked.
Easier said than done.
First of all you should collect and structure everything you know about the password to be cracked, analyze the data and cut it down to the range of only most probable values. Then run a check. Modify the range with new input, set a new (extended) range of values and repeat the search.
Repeat the sequence a few times.
Of course it is no easy task to crack files with strong encryption. However with Passcovery solutions you at least get tools that are easy to use and which raise your chances for success.
Below is a list of program features that enable you to tune up the search limits (with examples):
- “Range” settings. This is a regular brute force attack. Cut the range of characters to only those that may be used in your password. This way you get rid of unnecessary guesses.
- Brute force with mask attack. Follow the usual procedure — specify the known part of your password and let the program find the remaining part.
- Extended mask attack (example). This one is an irregular, flexible type of a brute force attack. You specify a range of characters for each position in your password which enables you to massively cut the number of checks.
- Mutation of dictionaries (example) . This is an extended dictionary attack. It allows merging dictionaries and setting word mutation rules which enables to use shorter dictionaries and makes the search run several times faster.
- Password recovery scenarios (example). With the help of this feature a search algorithm runs in accordance with the preset ranges. All you have to do is define a scenario, configure range settings and start the search. The program will follow through the “paths” step-by-step.
Last but not least, one of the strongest aces Passcovery has up its sleeve is an excellent search speed!
Best-in-class runtime speed. Both on CPU and GPU.
Try it! Download a demo version and give it a try.
Accent OFFICE Password Recovery
for Microsoft Office/OpenOfficeDownload x86
(10116 Kb)Download x64
(11688 Kb)
Accent PDF Password Recovery
for Adobe PDFDownload x86
(7208 Kb)Download x64
(8232 Kb)
Accent RAR Password Recovery
for RAR3/RAR5 archivesDownload x86
(11692 Kb)Download x64
(12728 Kb)
Accent ZIP Password Recovery
for Zip archives with classic/WinZip AES encryptionDownload x86
(7556 Kb)Download x64
(9028 Kb)
Passcovery Suite
for Microsoft Office, OpenOffice, ZIP, RAR, TrueCrypt, Apple iOS, BlackBerry OS, WPA/WPA2Download x86
(18912 Kb)Download x64
(21172 Kb)
